
29 Nov ICS Achieves SOC 2 Certification
Information and data security are the lifeblood of any organization, and it goes without saying that these valuable assets need to be protected at all costs. Information security is a reason for concern for all organizations, especially those that outsource key business operations to a third-party vendor, say a mailroom, scanning, and data capture vendor such as ICS. Mishandled data can leave an enterprise vulnerable to breaches and attacks, a nightmare that no management staff wants to ever deal with. As ICS continued to grow as a leading claims outsourcing vendor we understood this concern of our customers and set out to ensure that we took every step possible to safeguard the valuable information and data we handle in-house. ICS is proud to announce that as of November 2018 we have achieved our SOC 2 Type I and II compliance.
What is SOC 2?
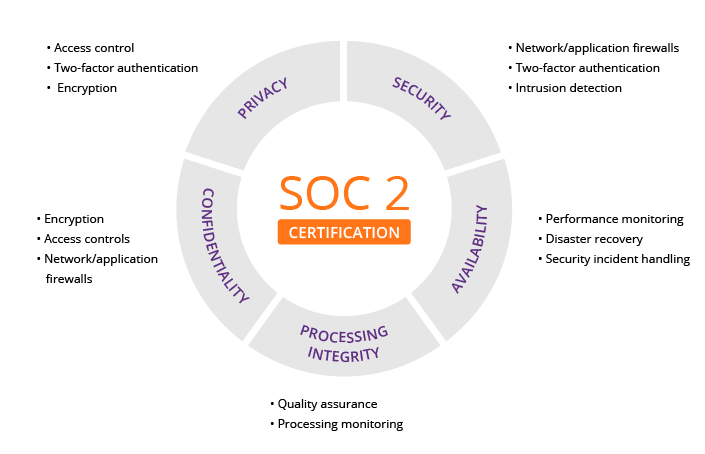 In short, SOC 2 (which stands for Service Organization Control) is an auditing procedure to ensure service providers securely manage and protect the data of its customers. SOC 2, developed by the AICPA, defines the criteria for managing customer data based on five trust service principles – security, availability, processing integrity, confidentiality, and privacy.
In short, SOC 2 (which stands for Service Organization Control) is an auditing procedure to ensure service providers securely manage and protect the data of its customers. SOC 2, developed by the AICPA, defines the criteria for managing customer data based on five trust service principles – security, availability, processing integrity, confidentiality, and privacy.
To meet SOC 2 requirements ICS had to prove it established and followed strict information security policies and procedures encompassing the five principles noted above. The SOC 2 certification is issued by an outside auditor, they ensured that ICS’ security measures were in line with the unique parameters of today’s service provider requirements. ICS underwent 2 separate audits spanning nine months in 2018 to achieve its’ SOC 2 type I and II certifications. We set out in 2018 to prove to our customers we were dedicated to providing them with the highest level of quality, service, and security that was possible. We feel this achievement is a tremendous step in the right direction that will allow us to serve our current and future customers with the proper securities, so they can rest assured their data is in good hands.

Sorry, the comment form is closed at this time.